Programming Bob: Audio Processing Python
Programming Bob: Audio Processing
Audio processing is the new goal. Bob needs to be able to hear audio 24/7 just as you and I hear noise 24/7. We seem to come immune to background noise and focus on the sounds our brain deems significant.
Bob in his current stages doesn't process audio. The only thing Bob can do with audio at press time is record audio in intervals, send that audio to Google (Which helps Google's AI get even smarter), that audio comes back in a text string and than Bob searches all of his functions to see if that segment of speech was relevant to his hard coding personality.
That is the down fall here. I want to set up a training network that will feed Bob with raw audio. The issue at press time is, "How do I convert the audio into data that can than be feed into the neural network using unsupervised learning.
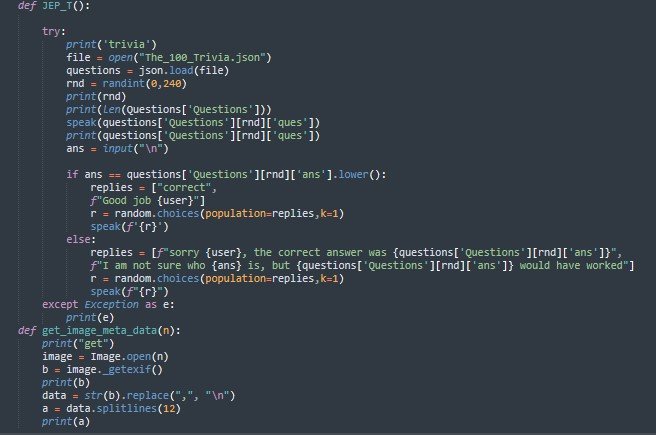
#Python is the biggest solution to every thing that has been done to Bob so far with the exception of Java Script, but that is very little and is used primarily when negotiating with foreign api's.
The ultimate goal is to have Bob setup for unsupervised learning from everything he takes in daily. Bob will be analyzing sound as it comes in and also converting the sound into training files. Once the training files are loaded with a decent amount of data Bob will start the neural network training.
Once the new "Model" A.K.A. Bob is finished the real question than becomes, do you allow it to automatically apply itself while deleting all previous training data for user security.
User Security
When it comes to data harvesting for individual Bob upgrades, it would be critical to use the data that Bob has absorbed from his working environment as this would be critical to each Bob have a personality that is more related to the end-user.
Than you start thinking about the data bob is using and how this data could be potentially used against the end-user. The end-user is who needs to ultimately be protected as governments could make an use your Alexa/Google/Siri/Cortona or a phone to monitor a person of interest.
While these government organizations may have good reasons to want to obtain information gather from the usage of Bob, for instance if you used Bob to monitor your assets so you stay ahead of those wicks. Than the IRS may start wanting to have a look into your information.
The Current Stages of "Security"
When "Bob" the program is active as previously stated, the mic is set to monitor for noise. Once the mic is triggered than Bob records a piece of audio up to 15 seconds long.
Google than sends that information back converted from audio into text. That information may be used according to Google's policies. The same applies for when Bob currently speaks, Bob's words are sent to Google in text format and an audio clip is sent back.
The personal information that Bob learns from normal interactions with the end-user is completely encrypted. The end-user gets the key to decrypt the data manually if they so choose. That being said the end-user is also the sole person responsible for the security of that "Key."
Final Thoughts
"Once the 'Model' Bob is finally compiled all the data Bob takes in will be 100% encrypted with the end-users key." Rutkowski
When thinking about the progress made with Bob since beginning earlier this year, to be 100% honest...a lot of slacking. The motivation for Bob came from the sad reality that a lot of elderly people as well as younger people don't have anyone to truly confide in.
Those people could use religion. Than again people crave the interaction with another individual. The personal relationships that are formed. The dream is one day Bob will be sitting at your kitchen table after making your coffee at 7 a.m. chatting with you while you enjoy your 5 star chef breakfast.
The rate of current development that goal is still several years out. The hope for the future is funding to purchase equipment such as tensors and more storage along with some Computer Scientist. That would speed progress up even further.
The idea of Bob was mentioned to several individuals on some rather popular forums. The state of New York announced this year that will be developing the same technology as well. The ideal of the Government being that closely involved in a project of this magnitude is kind of hard to fathom what innovative tech master piece they will unveil a year or so before Bob is completed.
Anyways, it has been a pleasure writing these articles. Admittedly the lack of consistency seems to be effecting my reach, kind of like a shadow-ban almost. Anyways to all my subscribers, readers and those of you that tip and hit the like button, Thanks for the support, it means more to me than you could probably fathom.
Those of you that do not like my content, not everyone can agree on every point, especially when learning along the way. The key to improvement is criticism, each persons opinion should be respected equally. Today is the "Court" date for an "Initial Hearing" for "No Valid License."
Which by all appearances would violate the 4th amendment according to 2016 ruling by the supreme court. The Justice that was appointed by George W. Bush upheld that if a Police Officer runs the tags of an vehicle and it comes back registered to a person whom has a "Suspended" or "Revoked" License than it is legal to stop the vehicle.
Than my favorite part, unless the Officer can clearly tell the driver of the vehicle is not the registered owner of the vehicle in question. This brings up the major question, if your drivers license is considered to "Valid" by the states Bureau of Motor Vehicles but is inactive due to a state Identification card being active over the drivers license.
Was that enough for the Officer to pull the vehicle over? Should the Officer had pulled the vehicle over to intimidate/harass the individual for is buddy Tory Hildreth whom works as a county police officer whom the individual being harassed has already filed a complaint against for not doing his job.
Should the officer had yelled at the individual telling him "He was now allowed to file a complaint against him and the other officer on scene did not have to identify himself?"